First set of presentations to whet your appetite
The first set of accepted presentations have been announced and they are packed with awesome++
Swiping Through Modern Security Features
Members of the elite Evad3rs jailbreak team including MuscleNerd, pod2g, planetbeing and pimskeks will be back in Amsterdam where they present their work on the iOS 6.1 public jailbreak, evasi0n, in which a total of 8 vulnerabilities in iOS were uncovered.
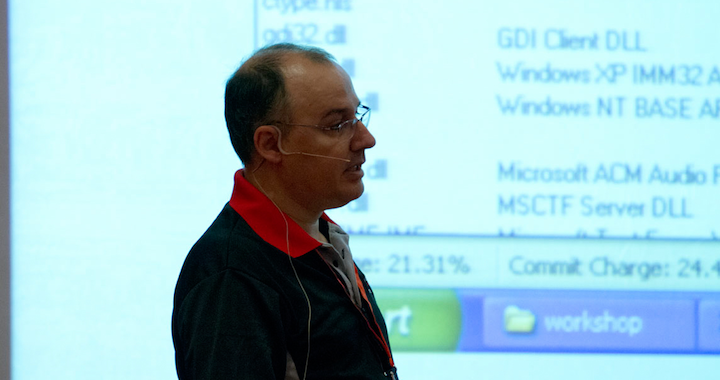
Exploiting Hardcore Pool Corruptions in Microsoft Windows Kernel
A technique of 100% reliable exploitation of kernel pool corruptions which covers all flavors of Windows from NT 4.0 to Windows 8.
How I Met Your Modem: Advanced Exploitation & Trojan Development for Consumer DSL Devices
An in-depth explanation of vulnerabilities found in consumer DSL devices which leads to a successful and reliable local and remote exploitation without user interaction.
Paparazzi Over IP
A newly discovered weakness in Canon cameras allows for complete control of the camera leading to an image stealing, Man-in-the-Imageflow.
SSRF PWNs: New Techniques and Stories
Server request forgery attacks – SSRF (Server Side Request Forgery) has been known since 2008, but only recently used in practical information security work. Vulnerabilities of this class gives the attacker the ability to send different requests on behalf of the server, which in turn allows you to bypass various network perimeter restrictions. Part of this presentation will be dedicated to the story of an SSRF-based total PWN of Yandex – a leading Internet company in Russia.
Aircraft Hacking: Practical Aero Series
This presentation will be a practical demonstration on how to remotely attack and take full control of an aircraft. Need we say more?
_______________
Follow @HITBSecConf on Twitter as we’ll be announcing more speakers in the coming days.
Online registration is here: http://conference.hitb.org/hitbsecconf2013ams/register/
_______________