Edward Schwartz’s Keynote & More Conference Goodies
The second round of presentations have been announced and Edward Schwartz, Chief Information Security Officer at RSA has also confirmed details of his keynote presentation. Titled “Embracing the Uncertainty of Advanced Attacks with Big Data Analytics“, Mr. Schwartz discusses how big data approaches can reduce uncertainties in succeeding against advanced adversaries by transforming four critical aspects of any security program.
And what new talks have made the list for the bash in April? Take a look…
Page Fault Liberation Army Or Better Security Through Creative x86 Trapping
Sergey Bratus and Julian Bangert from Darthmouth University college explore the inner workings of x86 processors. While the rest of the world programs only the x86 CPU with the provided instructions, clever neighbours like the PaX team instead program the MMU (Memory Management Unit) to enforce security policy. Sergey and Julian will show that the MMU is in fact a Turing-complete processor in its own right and demonstrate some tools that help to unleash its computational power.
SMS To Meterpreter: Fuzzing USB Internet Modems
Rahul Sasi of iSIGHT Partners focuses on an innovative new attack surface – USB Internet modems. He reviews the entire security architecture of USB data modems and the bugs found in various parsers and device drivers. In addition, he looks at the somewhat unexplored area of remote code execution via SMS.
Nifty Tricks and Sage Advice for Shellcode on Embedded Systems
Travis Goodspeed shows you how to write tiny shellcode that’s quickly portable to any variant of ARM, how to develop an embedded exploit without a debugger and how to blindly assemble a ROP (return-oriented programming) chain when you don’t even have the firmware image.
Orchestrating a Fire Sale: Bringing Dutch Alarm Systems to Their Knees
Wilco Baan Hofman provides an in-depth look at the SIA-HS and Vebon SecIP alarm system protocols in use in The Netherlands. He covers why these protocols are broken and how Dutch alarm systems can be rendered useless, creating panic at the alarm receiving centers and allows for a ‘Die Hard’ like scenario to be achieved.
In addition, two of the four HITB Lab sessions have also been confirmed – These intensive, hands-on 120 minute sessions form the third track in our triple-track line up and caters for only a maximum of 60 attendees.
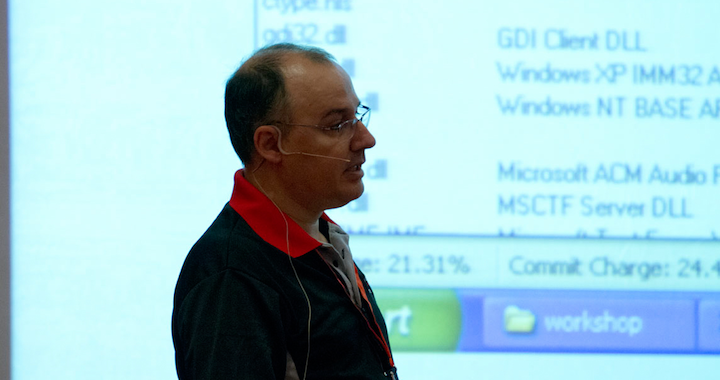
Windows x64: The Essentials
Didier Stevens touches upon important differences between 32-bit and 64-bit Windows in this lab session, teaching you nifty tricks like how to develop and inject an x64 DLL, how to develop x64 shellcode, how to ‘break out’ of WoW64 and much much more. A must attend for all Windows hackers.
Hack Like It’s 2013
Itzik Kotler introduces you to Hackersh with Pythonect – a powerful new tool in your hacker arsenal. Pythonect is a new, free, and open source general-purpose dataflow programming language based on Python, written in Python. Hackersh is inspired by the UNIX pipeline, but takes it a step forward by including built-in features like remote invocation and threads. This 120 minute lab session will introduce Hackersh, the automation gap it fills, and its features.
As always, the HITB Labs require audience interaction, so please bring your own laptops if you intend to attend. Seats are given out on a first come first serve basis so be sure to be at the track room at least 10 minutes before the session commences. Still haven’t registered yet? Better get going; conference seats are starting to fill up and prices increase after the 20th of March. Follow @HITBSecConf on Twitter or stay tuned to the #HITB2013AMS hashtag as there are more presentations to be announced!
___________________