TECH TRAINING 1 – THE EXPLOIT LABORATORY ADVANCED EDITION – #HITB2013AMS
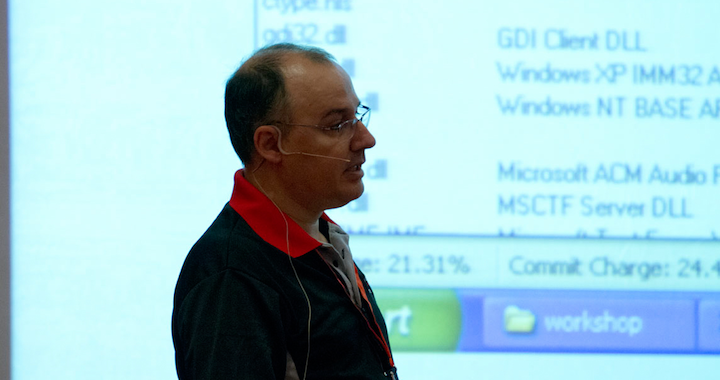
TRAINERS: Saumil Shah (Founder, Net-Square) and SK Chong (Security Consultant, SCAN Associates Bhd.) |
CAPACITY: 20 pax |
SEATS LEFT: REGISTRATION CLOSED
|
DURATION: 2 days (8th & 9th April 2013) |
COST (per pax): EUR1499 (early bird) / EUR1899 (non early-bird) |