What: Team-based Attack & Defense Capture the Flag organized by Hackerdom
When: 26th April, 10am – 6pm CET
Where: Online
Download VulnImage: https://vpn.hitb.org/ova/hitblockdownctf.ova.gpg
Decryption Key: RAREr7LZo6EfxDCd
This is a “special edition CTF” with some services from previous competitions that were not exploited. Get ready for that good old “nostalgia feelz”
LIVE STREAM /
REGISTERED TEAMS /
- dirtyB1t (USA)
- the3000 (Tunisia)
- H0j3n (Malaysia)
- Scorpions (India)
- Noob (Malaysia)
- SKR (Malaysia)
- cyber defecers (India)
- icebreak (Russia)
- QuePasaZombies (International)
- TCSC [Tamil Cyber Security Council] (India)
- noobwinjateam (India)
- http.deep (India)
- The Zappers (Netherlands)
- cod.group.ir (Iran)
- BambooFox (Taiwan)
- Catamob (India)
- nganggur (Indonesia)
- Th3NewNormal (Netherlands)
- Eat Sleep Pwn Repeat (Germany)
- saarsec (Germany)
- Spotless (Netherlands)
- condor (India)
- The Black Widow (Nigeria)
- ParaTroopers (India)
- :Duurtlang (Netherlands)
- cipher (Singapore)
- Sudo_root (Algeria)
- STT (Portugal)
- Alt-Backdoor (UAE)
- HuntsvilleTechSupport (USA)
- MOKA (South Korea)
- Cyber Paladins (Singapore)
- Tipi’Hack (France)
- Cyber Offence Center (Germany)
- dedsec (UAE)
- BadBuddy (USA)
- Lauren New (USA)
- Root (India)
- ayam (Malaysia)
- IamgRoot (Netherlands)
- Avengers_l33ts (Netherlands)
- Fword (Tunisia)
- cahkerjo (Indonesia)
- Xyber Paladins SG 133713pwnies (Netherlands)
- APT69 (UK)
- CloudEmpire (Malaysia)
- Trailbl4z3r (Malaysia)
- EGInit-0 (Egypt)
- MorningPlop (France)
- team7even (Algeria)
- FooBar (India)
- 0xN1ghtRa1d (Egypt)
- PDKT (Indonesia)
- LEGOFAN (Germany)
- CTFO (France)
- dcua (Ukraine)
- coalore (China)
- AFK (Thailand)
- The Duck (South Korea)
- $@mur@! (UAE)
- DHA-Dream_Team (USA)
- CDL_Dream_Team (USA)
- degen sleep squad (International)
- Cavalletto (Italy)
- CyberKnight00 (India)
- D.I. (South Korea)
Slack Channel: https://hitblockdown.slack.com/join/shared_invite/zt-dp5n7pid-KWBkWGt~mDtB7geSzhhGiQ
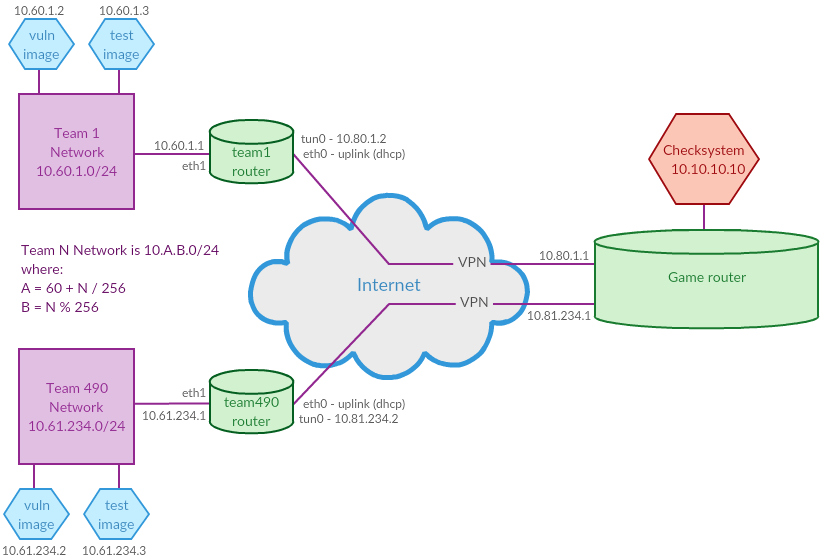
NETWORK SCHEME /
SET UP VIRTUAL MACHINES /
- Install VirtualBox.
- Download router and test images
- Check SHA256 sums:
- 76db7a40e0717a197fdd30d2b271006bf7f18768fd0ddd5e1693a142098bc460 hitb_lockdown_ctf_2020_router.ova
- bd0c672a5210477a53f389cdc86c0fed0c80d0f492f2c340b08654c13b598626 hitb_lockdown_ctf_2020_testimage.ova
- Import both images to VirtualBox: “File->Import Appliance…
- Check router image settings. Go to: “Settings->Network->Adapter2”. Make sure that it is bridged to your real, hardware network adapter. It is preferable to use Ethernet adapters for bridging rather than Wi-Fi adapters.
- Check test image settings. Make sure that Adapter1 is bridged to your real network adapter.
- Start both virtual machines. You will see some instructions on a logon screen.
- Follow instructions on the logon screen and enter your team number to configure the network:
router image:
eth0 – this is your uplink. Address is obtained via dhcp by default. This interface is attached to NAT in VirtualBox, so make sure that you have an internet connection on your physical host;
eth1 – this is your internal interface. It should be automatically set to: 10.60.N.1.
test image:
eth0 – it should be automatically set to: 10.60.N.3 and gateway: 10.60.N.1 - You should use following network settings for your team’s PCs during the game (or virtual machines setup):
IP = 10.60.N.128 - 10.60.N.255 Netmask = 255.255.255.0 Gateway = 10.60.N.1 DNS = 8.8.8.8
SET UP VPN CONNECTION /
- Follow the instructions sent on your PoC email (if not, please send message to: bay@hackerdom.ru) to obtain your OpenVPN config.
- Copy the config to /etc/openvpn/*.conf (for example to /etc/openvpn/hitblockdown.conf).
- Restart OpenVPN on your router (service restart openvpn@hitblockdown if your confing has name hitblockdown.conf).
- Check network connectivity. You should be able to ping 10.80.N.1 from your router and testimage (N is your team ID). Check your connection status at http://vpn.hitb.org/ (all tests for your team should pass, the page updates once in a few minutes)
- Leave both images running. You can shut down your testimage when the game starts.
RULES /
First of all, the aim of this challenge is not to find out who is the best team. We sincerely believe that true professionals are incomparable. The main goal of HITB Lockdown CTF is to share experience and knowledge in the computer security and to have some fun together. Nevertheless, the luckiest team will become a winner. It is difficult to give a complete set of rules for a CTF challenge, so these rules can change at any moment before the challenge starts. That is why we recommend you to check the rules on this site one more time before the competition starts. Just in case 🙂
DEFINITIONS /
TEAM /
A group of people with a captain.
SERVICE /
A vulnerable application written for the challenge.
FLAG /
A string that matches regex: /^\w{31}=$/.
GAME ROUND /
A period of time for checksystem to check and score all the teams. It usually takes about 1 minute.
ORGANIZERS /
A group of people that run the whole competition. Organizers do their best to provide quality and fun to all participants. Still organizers are to penalize/disqualify teams for rules violation and to solve the critical situations not described in these rules. Teams should be prepared to meet such decisions with understanding. Also organizers do determine the winner. In general, this decision is based on the scoreboard.
TEAMS ARE ALLOWED TO /
- Do whatever they want within their network segment. Most likely the team would like to patch vulnerabilities in their services or block exploitation of vulnerabilities;
- Attack other teams. Didn’t expect that, huh?
TEAMS ARE PROHIBITED FROM /
- Filter out other teams’ traffic;
- Generate large amount of traffic that poses a threat to network stability of organizers’ facilities;
- Generate large amount of traffic that poses a threat to network stability of any other team;
- Attack teams outside of the VPN;
- Attack the game infrastructure facilities operated by organizers.
GAME STRUCTURE /
The competition begins when the organizers announce vulnerable image decryption key. Since then the whole game time is divided into two periods:
- For the first hour network segments are closed and teams should concentrate on initial vulnbox administration and vulnerabilities analysis.
- For the next 7 hours network segments are opened.
SCORING SYSTEM /
Key params in scoring system are SLA and FlagPoints. Their values are individual for each service of each team. Team’s score is calculated as the sum of the products of the corresponding SLA and FlagPoints of all team’s services.
SLA (team, service) is the percentage of the game time, during which that service of that team was in the UP state. E.g. if the service was always UP, SLA would be 1. If 4 hours passed from the game start and the service was up only during the first hour and then was not UP for the rest 3 hours, SLA would be 0.25. At the beginning all teams have SLA equal to 1.
FlagPoints (team, service) – is the number that correlates with team’s ‘understanding’ of the service. If the team is able to exploit the vulns in the service to get flags and fixes these vulns in it’s own service, the FlagPoints will grow during the game. Otherwise, if the team is not able to exploit the vulns in service and to fix them in it’s own service, FlagPoints will decrease during the game but will never fall down to 0. If the team can only fix vulns but not exploit them, it’s FlagPoints will not change. At the beginning all teams have equal FlagPoints.
Flag’s price is the number of FlagPoints got by attackers for stealing the flag from the victim.
Flag’s lifetime is the amount of time during which the flag should be available in the service for checksystem. At HITB Lockdown CTF it’s 15 rounds. Teams should steal the flag and post it to checksystem until it is expired.
FlagPoints (team, service) decreases by the maximum value equal to the number of the teams for each stolen flag.
FlagPoints (team, service) If the flag was stolen from a team that was higher on the scoreboard in the previous round, the team that has stolen the flag earns the maximum number of FlagPoints(which is equal to the number of teams, as it was mentioned). If flag was stolen from a team that was below your team on the scoreboard, the number of FlagPoints will decrease exponentially down to 1.
FlagPoints score at the moment of each flag’s expiration.
Luckily all this complex text can be expressed in pseudocode:
def on_game_start(team):
team.sla = [1] * number_of_services
team.flagpoints = [0] * number_of_services
def on_flag_post(attacker, flag):
victim = flag.owner
victim_pos = scoreboard[victim]
attacker_pos = scoreboard[attacker]
service = flag.service
max = number_of_teams
flag_score = attacker_pos > victim_pos ? max : exp(log(max) * (max - victim_pos) / (max - attacker_pos))
attacker.flagpoints[service] += flag_score
victim.flagpoints[service] -= min(victim.flagpoints[service], flag_score)
def get_score(team):
return sum(map(lambda x: x[0] * x[1], zip(team.sla, team.flagpoints)))
SCOREBOARD /
During the game, scoreboard will be available at http://scoreboard.hitb.org/
You can submit your flags to https://scoreboard.hitb.org/flags
Teams are ranked by total score.
Apart from FlagPoints, SLA and total score, scoreboard shows statuses of each service. Statuses are as following:
- OK — means that service is online, serves the requests, stores and returns flags and behaves as expected.
- MUMBLE — means that service is online, but behaves not as expected, e.g. if HTTP server listens the port, but doesn’t respond on request.
- CORRUPT — means that service is online, but past flags cannot be retrieved.
- DOWN — means that service is offline.
HTTP flag submiting example /
$ curl -s -H 'X-Team-Token: your_secret_token' -X PUT -d '["PNFP4DKBOV6BTYL9YFGBQ9006582ADC=", "STH5LK9R9OMGXOV4E06YZD71F746F53=", "0I7DUCYPX8UB2HP6D6UGN86BA26F2FE=", "PTK3DAGZ6XU4LPETXJTN7CE30EC0B54="]' http://scoreboard.hitb.org/flags | json_pp
[
{
"msg" : "[PNFP4DKBOV6BTYL9YFGBQ9006582ADC=] Denied: no such flag",
"status" : false,
"flag" : "PNFP4DKBOV6BTYL9YFGBQ9006582ADC="
},
{
"msg" : "[STH5LK9R9OMGXOV4E06YZD71F746F53=] Denied: flag is your own",
"flag" : "STH5LK9R9OMGXOV4E06YZD71F746F53=",
"status" : false
},
{
"status" : false,
"flag" : "0I7DUCYPX8UB2HP6D6UGN86BA26F2FE=",
"msg" : "[0I7DUCYPX8UB2HP6D6UGN86BA26F2FE=] Denied: you already submitted this flag"
},
{
"msg" : "[PTK3DAGZ6XU4LPETXJTN7CE30EC0B54=] Accepted. 1.73205080756888 flag points",
"flag" : "PTK3DAGZ6XU4LPETXJTN7CE30EC0B54=",
"status" : true
}
]

