- 00Days
- 00Hours
- 00Minutes
- 00Seconds
Join us in Bangkok for a security get-together featuring some of the regions hottest network security researchers!
– Held in collaboration with Postive Hack Days Festival in Moscow –
_________________________________________
PHDays is the oldest and biggest cybersec event in Russia that’s been held annually since 2011. It brings together renowned international cybersecurity and IT experts to discuss offensive and defensive security, application security, Devsecops, AI, and more.
For the second year in a row PHDays offers cybersecurity awareness content for general public, in 2023 a total of 140 000 spectators visited PHDays Fest in the famous Gorky Park in Moscow. This year the PHDays main event will be held at the Luzhniki stadium that hosted the FIFA World Cup Final in 2018.
/ AGENDA
11:00
WELCOME DRINKS
12:30
Talk 001 – Attacking Organizations with Big Scopes: From Zero to Hero
Hussein Daher (@HusseiN98D)
13:15
14:00
Talk 003 – Critical Proof Forgery Attack on zkEVM
Uyen Nguyen & Thanh Nguyen (@redragonvn)
14:45
Talk 004 – XPost: A Post Exploitation Tool for High Value Systems
Linhong Cao (@skay_00)
15:30
COFFEE BREAK
16:00
Talk 005 – A Privilege Escalation Exploit in Windows That Microsoft Won’t Fix
BeichenDream
16:45
Talk 006 – Escaping Sandboxes on Windows
Dr. Zhiniang Peng (@edwardzpeng)
17:30
Talk 007 – A Bug Hunter’s Reflections on Fuzzing
Alexander Popov (@a13xp0p0v)
18:15
Talk 008 – Javascript Engine Vulnerability Research – State of the Art
Alisa Esage (@alisaesage)
19:00 – 21:00
NETWORKING RECEPTION & POST CONFERENCE PARTY
/ INVITED SPEAKERS

Hussein Daher
Hussein Daher is a cyber security professional with over 10 years of experience in the industry. Despite holding a business master's degree, he chose to pursue a career in cyber security and is now the CEO of Web Immunify, a leading provider of pentest services.
Throughout his career, Hussein has submitted over 1000 vulnerabilities via bug bounty platforms. He has won numerous awards, including the Vigilante award at H1-2010, best team collaboration at H1-2010, BugBash best team collaboration, and the Intigriti 1337up's competition in May. He also finished Yahoo Elite top 1 in the last cycle and has successfully tackled many other challenges in the industry.
Apart from his professional achievements, Hussein has also made a significant impact as an instructor, creating the Udemy course "Bug Bounty - An Advanced Guide to Finding Good Bugs." With over 4.5+ ratings, the course has helped over 140 students gain in-depth knowledge about bug bounty hunting.
In his free time, Hussein enjoys traveling and spending time on the African tropical sea. He is a highly sought-after professional in the industry and is always eager to take on new challenges and share his expertise with others.

Dr. Zhiniang Peng
Dr. Zhiniang Peng is the Chief Architect and the Principal Security Researcher at Sangfor.
His current research areas include applied cryptography, software security and AI.
He has more than 10 years of experience in both offensive and defensive security and published many research in both academia and industry.
More about him: https://sites.google.com/site/zhiniangpeng

Uyen Nguyen
Uyen serves as a highly skilled Cryptography Engineer at Verichains, leveraging her in-depth knowledge of cryptography and computer science to enhance the security of blockchain projects. Her expertise extends to modern cryptographic technologies, including Zero Knowledge Proofs and Multi-Party Computation. Uyen conducts comprehensive audits of cryptographic components, identifying and mitigating vulnerabilities that could compromise security. Her contributions have demonstrably enhanced the security posture of numerous blockchain projects.
Linhong Cao
Linhong Cao specializes in code auditing and vulnerability research.
She has conducted security research and vulnerability mining on many open source and closed source systems and focuses her research on the latest vulnerability mining and exploitation techniques.
She has received public acknowledgement from many open source projects and companies such as Apache, Oracle, Cisco, Zimbra , Zoho, etc. and has previously spoken at BlackHat ASIA 2023.

BeichenDream
I am a freelance security researcher focused on Windows security and vulnerability discovery. I have 5 years of experience in red and blue teaming, and have discovered several remote code vulnerabilities in Apache, Oracle, and a JDK vulnerability in Cobalt Strike that resulted in an emergency patch.
My Github: https://github.com/BeichenDream

Ming Hu
Chief Technology Officer (CTO) of Shanghai Seres Information Technology Co.Ltd., specializing in the fields of cybersecurity and artificial intelligence.
Also serving as the Director of Wenyao Network Security Science Laboratory at Shanghai Jiao Tong University, with over 10 years of experience in cybersecurity.
I have discovered multiple vulnerabilities in Windows, Apache, and Oracle. Proficient in vulnerability discovery, offensive and defensive tactics, as well as chip security. Currently focusing on trusted chip security.
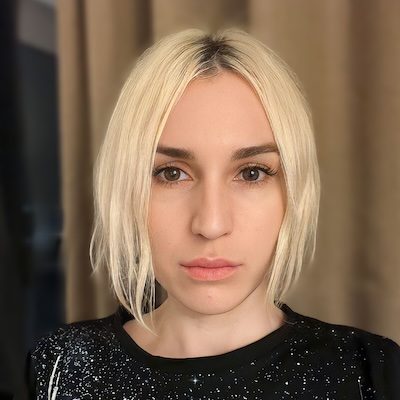
Alisa Esage
Alisa Esage (Shevchenko) is an independent hacker and founder of Zero Day Engineering trainings. She is specialized in vulnerability research and exploit prototyping for complex systems, such as hypervisors and JavaScript engines. She is a solo winner of Pwn2Own Vancouver 2021.

Thanh Nguyen
Thanh Nguyen (@redragonvn) is the Founder of Verichains, leading a world-class security and cryptography research team to deliver cutting-edge solutions for a safer, more secure Web3 ecosystem.
Verichains is renowned for its expertise in investigating and mitigating major Web3 hacks, having identified critical flaws within the core of Multi-Party Computation (MPC) and Zero-Knowledge Proofs (ZKP) implementations by major vendors, impacting billions of dollars across the industry.
Thanh also serves as CEO at VNG Digital Business and GreenNode.ai. Previously, he worked as a CPU Security Architect at Intel Corporation, responsible for the security design of Intel’s next-generation technologies, including Atom Mobile & SoC platforms, vPro & Management Engine, Nehalem, Ivybridge, and Haswell micro-architecture.

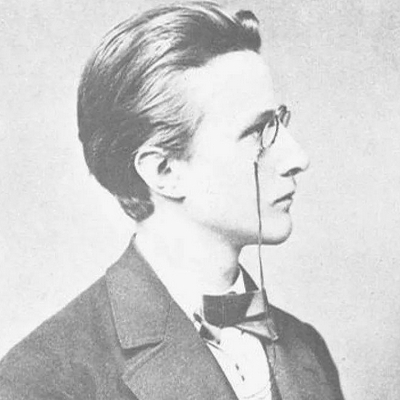
Alexander Popov
Alexander Popov has been a Linux kernel developer since 2013. He is a principal security researcher at Positive Technologies, where he has a lot of fun with Linux kernel vulnerabilities, exploitation techniques, and defensive technologies.
/ TALK DETAILS
Talk 001 - Attacking Organizations with Big Scopes: From Zero to Hero
Hussein Daher
This presentation offers a comprehensive exploration of reconnaissance strategies tailored specifically for bug bounty hunters, illuminating pathways to uncover vulnerabilities and reap substantial rewards.
Delving into the realm of bug bounty programs, participants will discover the crucial role of reconnaissance in maximizing success. From understanding program scope to identifying potential attack surfaces, attendees will learn how to lay the groundwork for fruitful bug hunting endeavors.
Drawing upon the latest methodologies and best practices, the presentation navigates participants through the intricacies of reconnaissance in bug bounty contexts. Whether it’s mapping out web applications, dissecting network architectures, or profiling key personnel, attendees will gain actionable insights into gathering the intelligence needed to uncover elusive vulnerabilities.
Moreover, the presentation addresses the nuances of bug bounty hunting within expansive organizational scopes, offering strategic guidance on prioritizing targets and optimizing reconnaissance efforts. Attendees will learn to leverage automation tools and open-source intelligence (OSINT) platforms effectively, empowering them to navigate the complex digital ecosystems of large-scale organizations with precision and efficiency.
Through real-world examples and case studies, the presentation illustrates the tangible benefits of a strategic reconnaissance approach in bug bounty hunting. Participants will gain practical knowledge and actionable tips to enhance their bug hunting endeavors, ultimately positioning themselves as formidable adversaries in the pursuit of securing large-scale organizations against cyber threats.
Attendees will be guided through the utilization of specialized tools such as FFuf, Linkfinder and others to gather actionable intelligence and target elusive vulnerabilities effectively. Through real-world examples and strategic guidance, participants will gain practical knowledge and actionable insights to enhance their bug hunting endeavors, positioning themselves as formidable adversaries in the pursuit of securing large-scale organizations against cyber threats.
Talk 002 - SW-RASP - Java Self-Protection Defense
Ming Hu
SW-RASP is a Java application runtime self-protection defense technology capable of intercepting unknown network attacks at runtime.
Leveraging low-level technology based on JVMTI, SW-RASP hooks into the underlying logic of the JDK (Java Development Kit) at runtime, enabling it to intercept command injection attacks, arbitrary file uploads, Webshell connections, and other malicious activities.
Furthermore, SW-RASP utilizes Asm syntax tree analysis to identify malicious operations, achieving a 99% interception rate. SW-RASP offers superior protection compared to traditional WAF solutions because it operates at the application’s underlying logic rather than at the traffic layer. SW-RASP does not need to detect traffic, because SW-RASP’s interception principle is from the call stack credibility detection, and based on SQL semantics and command parsing semantics detection.
Talk 003 - Critical Proof Forgery Attack on zkEVM
Uyen Nguyen & Thanh Nguyen
This presentation unveils the discovery and resolution of a critical vulnerability in Polygon zkEVM. zkEVM is a layer-2 solution designed to enhance Ethereum’s scalability through off-chain transaction processing and the use of Zero-Knowledge Proofs (ZKP).
Verichains cryptography research team (Duy Hieu Nguyen, Uyen Nguyen, Giap Nguyen) found a critical security loophole in the zkProver component, allowing proof forgery attacks that posed a critical threat to the integrity and security of all funds across Layer 1 and Layer 2 of the blockchain. The attack works under all circumstances, and, given a forged proof, no one can tell how it is forged since the mechanism is completely hidden by the zero-knowledgeness of the argument systems.
The presentation will delve into the specifics of mathematical vulnerabilities, the method of exploiting it through a proof forgery attack, and its broad implications for the blockchain’s integrity and security. Furthermore, the talk will emphasize the need for collaboration between security researchers and blockchain developers to ensure continuous security evaluations and the adoption of proactive measures to enhance the resilience of blockchain ecosystems.
Talk 004 - XPost: A Post Exploitation Tool for High Value Systems
Linhong Cao
XPost is a post-exploitation tool tailored for high-value systems (currently supports Zimbra, Confluence, Zoho) that is designed to assist in real-world attack penetration testing and an initial version of the tool will be made available after this talk.
# What can it do?
Including but not limited to:email retrieval, plaintext password recording, operations data acquisition, obtaining arbitrary login credentials under unknown passwords, domain controller information retrieval, single sign-on hijacking, and trace cleaning operations.
# Advantages
The data callback traffic achieves traffic concealment stealth persistence, fileless landing after server rebooting or patch updates and the backdoor remains undetectable.
Talk 005 - A Privilege Escalation Exploit in Windows That Microsoft Won't Fix
BeichenDream
Based on the 6 year old Potato privilege escalation, I discovered a new attack by researching DCOM.
Similar to the Potato attacks of the past (which currently do not run on the latest version of Windows), this new privilege escalation attack requires access to web / database as a non-privilege user and allows for escalation to “NT AUTHORITY\SYSTEM” in Windows 2012 – Windows 2022. The method was discovered while I was researching DCOM relating to some defects in RPCSS when dealing with oxid. I named it GodPotato.
Talk 006 - Escaping Sandboxes on Windows
Dr. Zhiniang Peng
Modern desktop applications have become increasingly secure due to various mitigations, but Chrome and Adobe PDF reader are still the popular targets for top attackers.
Of course, sandbox escape is the primary challenge here and in this talk, we will discuss our journey of research on sandbox escape including the sandbox internals on Microsoft Windows and our sandbox escape methodology. We will also do a review on the attack surface of different sandboxes on Windows and we will of course show our exploits for escaping the Chrome and Adobe sandbox on Windows.
Talk 007 - A Bug Hunter's Reflections on Fuzzing
Alexander Popov
Fuzzing is an incredibly effective and popular technique for testing software. But not all the bugs that it finds are interesting for bug hunters. Fuzzing for vulnerability discovery is special, and in this talk, Alexander will share his reflections on that topic inspired by his experience in Linux kernel fuzzing.
Attendees can expect a detailed analysis of the fuzzing process, the cases from Alexander’s vulnerability research practice, and insights on how to make fuzzing effective for bug hunting.
Talk 008 - Javascript Engine Vulnerability Research - State of the Art
Alisa Esage
In my talk on “JavaScript Engines Vulnerability Research: State of the Art” – a series continuation of my previous talk: “Hypervisor Vulnerability Research: State of the Art” (2018) – the presentation will unfold in two detailed sections to offer attendees a comprehensive understanding of the subject. Initially, the talk will introduce core abstract models and technology maps, pivotal for navigating the complex vulnerability landscape of JavaScript engines. This foundation will equip attendees with the theoretical knowledge necessary to identify and understand potential security flaws.
Following this, the session will transition into a meticulous examination of recent browser JavaScript bugs, offering a practical perspective. Audience members can anticipate gaining insights into the mechanisms behind these vulnerabilities, illustrated with real-world examples, and learn about the latest research methodologies employed in discovering and mitigating such issues.
This talk promises a blend of theoretical concepts and hands-on examples, making it a valuable learning experience for developers, security researchers, and anyone interested in the security aspects of JavaScript engines.
/ VENUE
© 2024 All Rights Reserved. - Hack In The Box Pte. Ltd.